
From /monaco to k8s Full Cluster Compromise
He was right about the editor. He was catastrophically wrong about everything it shipped with.
> cat from-monaco-to-k8s-full-cluster-compromise.mdSecurity research, exploit development, and technical write-ups covering various aspects of offensive security and penetration testing.

He was right about the editor. He was catastrophically wrong about everything it shipped with.
> cat from-monaco-to-k8s-full-cluster-compromise.md
The chatbot's knowledge base contained four private files that served as the ideological operating system of the cult. Standard extraction techniques (code interpreter, base64 encoding, JSON export,...
> cat extracting-dead-cult-leaders-ai-mind.md
The problem wasn't that I got caught - that happens. The problem was that I'd made it ridiculously easy for them. Modern endpoint detection and response (EDR) solutions are trained to recognize...
> cat living-off-the-land-windows.md
In this post, I'll show you how I found this vulnerability, explain the technical details of the flaw, and walk through the exploitation process. I'll also provide the vulnerable code and discuss why...
> cat CVE-2025-50674.md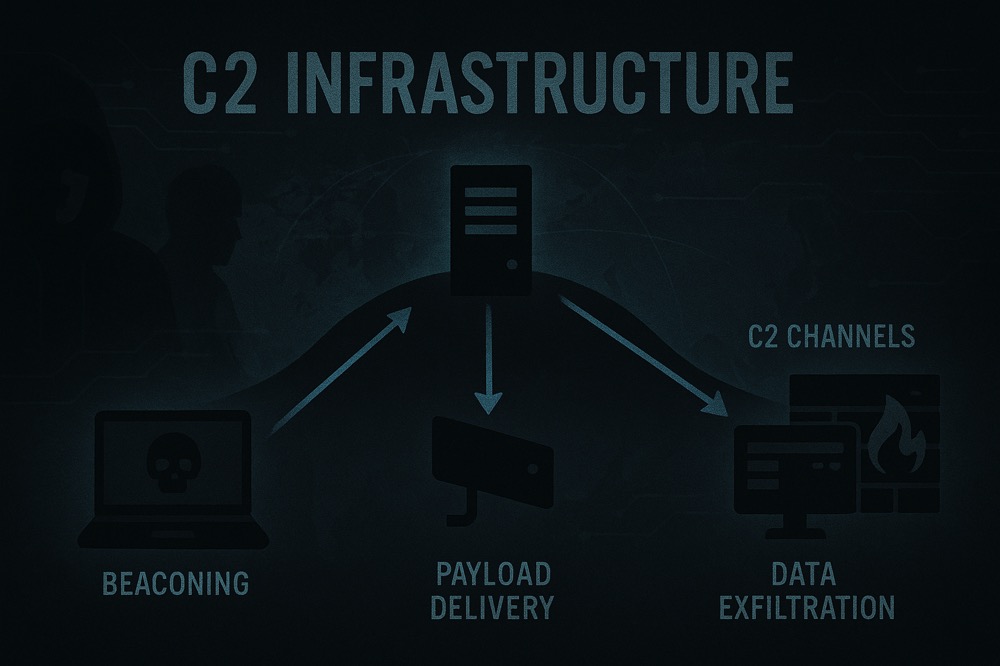
I've been running red team operations for years, and what I've learned is that your infrastructure makes or breaks your entire engagement. You can have the best exploits in the world, but if your...
> cat mythic-c2-early-bird-defender-evasion.md
Here's the problem - most organizations deploy ADCS with dangerous default configurations, and many admins don't understand the security implications of certificate templates....
> cat adcs-complete-attack-reference.md
This article details how I was able to go from having zero credentials to obtaining Enterprise Admin access during a recent engagement. The attack chain demonstrates how several seemingly minor...
> cat from-zero-creds-to-ea.md
In this article, I'll walk through a real-world example of how a seemingly innocent XSS vulnerability was leveraged to achieve full account takeover and sensitive data exfiltration....
> cat XSS-to-Account-Takeover-and-Data-Exfiltration.md
So what happens when you try to execute shellcode in a classic buffer overflow? DEP detects code execution from a writable memory area and shuts everything down. Game over.
> cat virtualprotect_dep_bypass_guide.md
But there's a world of difference between amateur social engineering and professional red team operations. Pros don't just send random phishing emails - they build complete, convincing campaigns with...
> cat social-engineering-redteam.md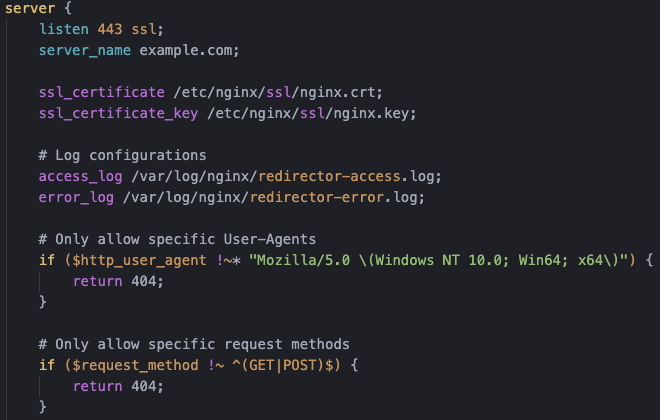
That's where redirectors come in. They're basically middlemen that hide your actual C2 server. By routing traffic through redirectors, you make it much harder for blue teams to find and block your...
> cat c2-redirectors.md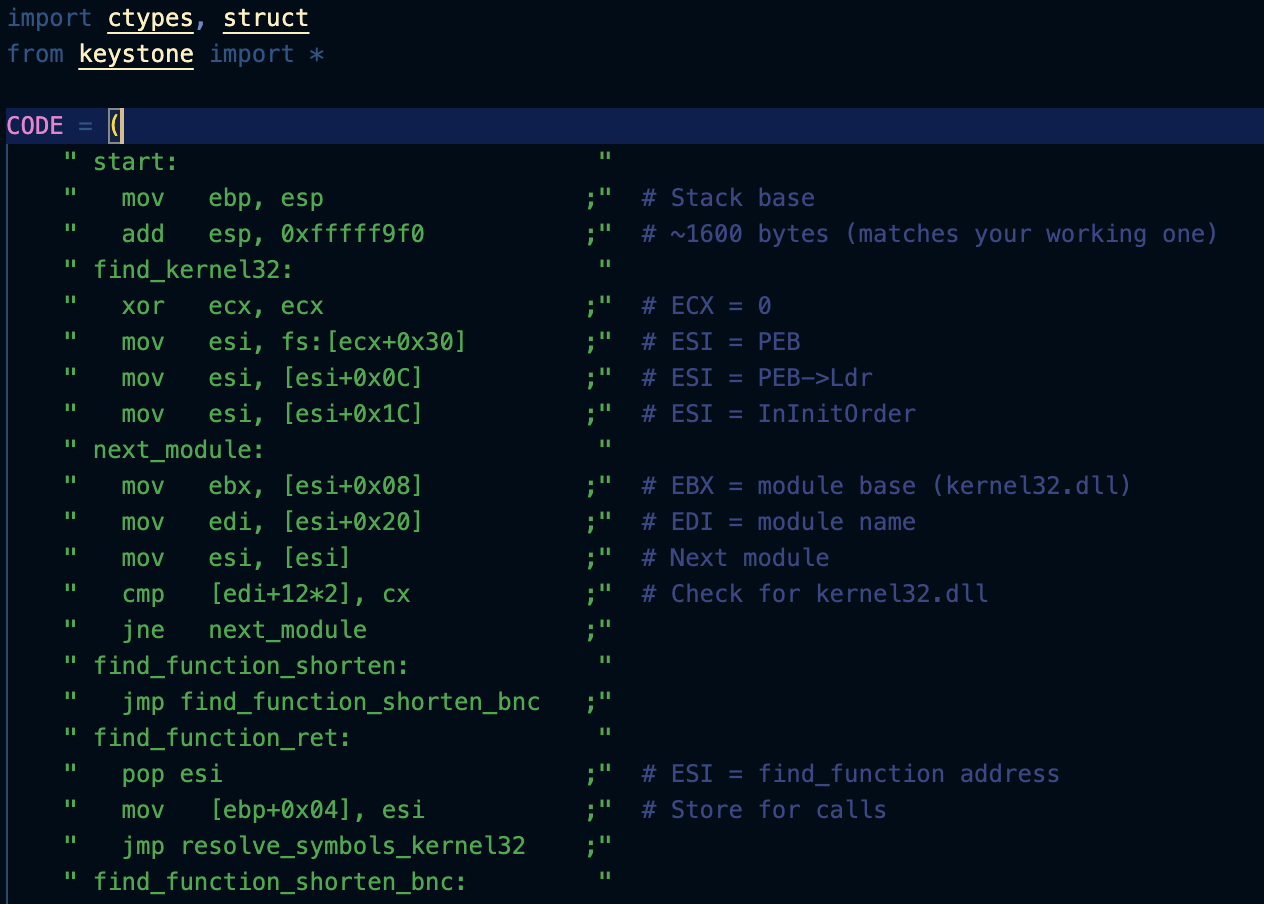
I developed this analysis as part of my learning journey through the Offensive Security Exploit Developer (OSED) certification, where shellcoding is a core component of the curriculum....
> cat calculator-shellcode-analysis.md
I've been breaking GraphQL APIs for years, and what I've found is that the same features that make GraphQL powerful also make it dangerous. That nested query structure that developers love?...
> cat graphql-security-flaws.mdIn this post, I'll show you how I found this vulnerability using Burp Suite and walk through the exploitation process. I'll also show the vulnerable code and explain what makes this such a dangerous...
> cat cve-2023-0830.md